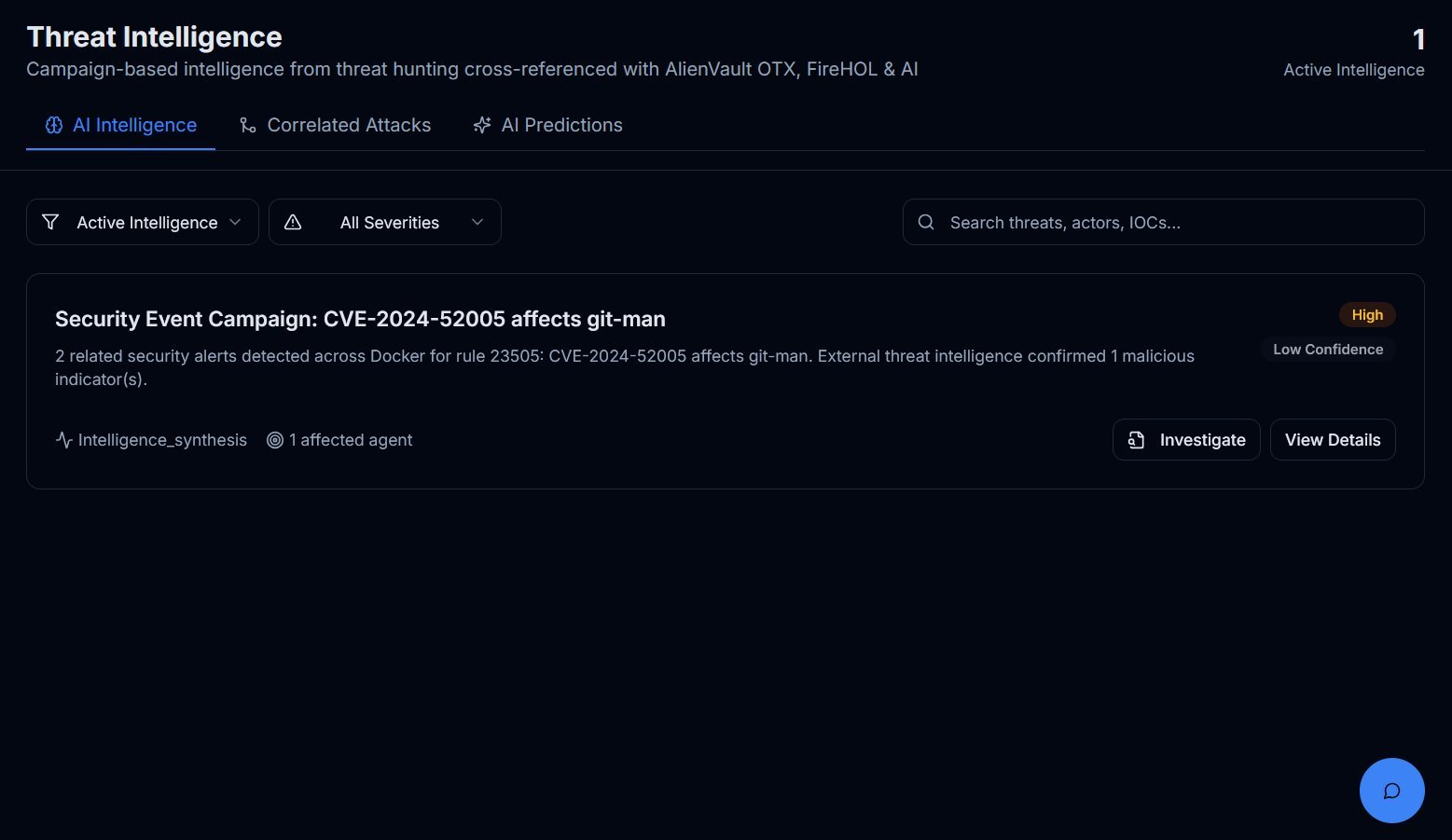
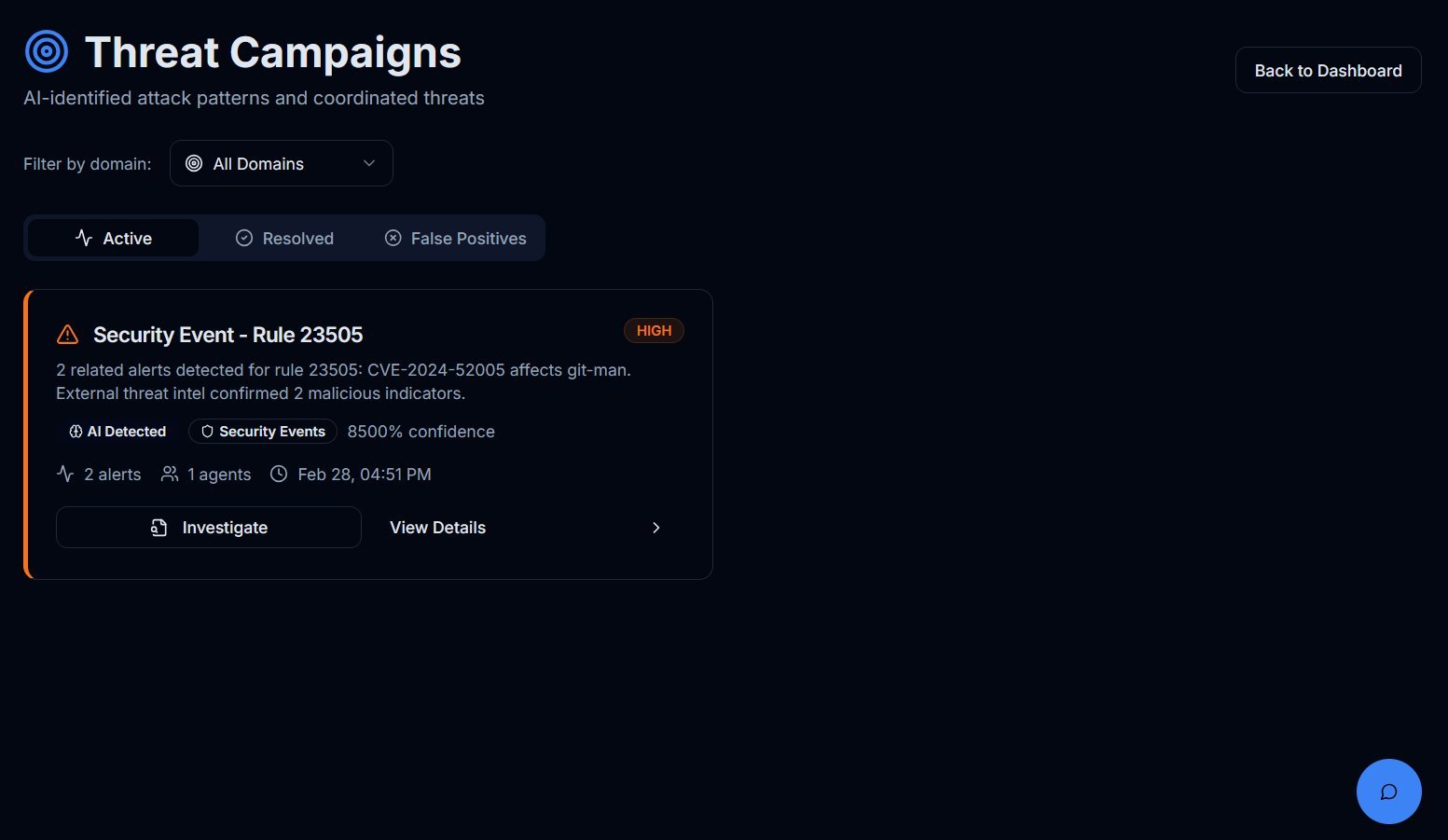
SecureSOC automatically correlates related alerts into threat campaigns, giving you a clear picture of active attacks with confidence scores, MITRE ATT&CK mappings, and affected assets — all in one view.
- Automated threat campaign correlation
- MITRE ATT&CK framework mapping
- Confidence scoring for prioritization
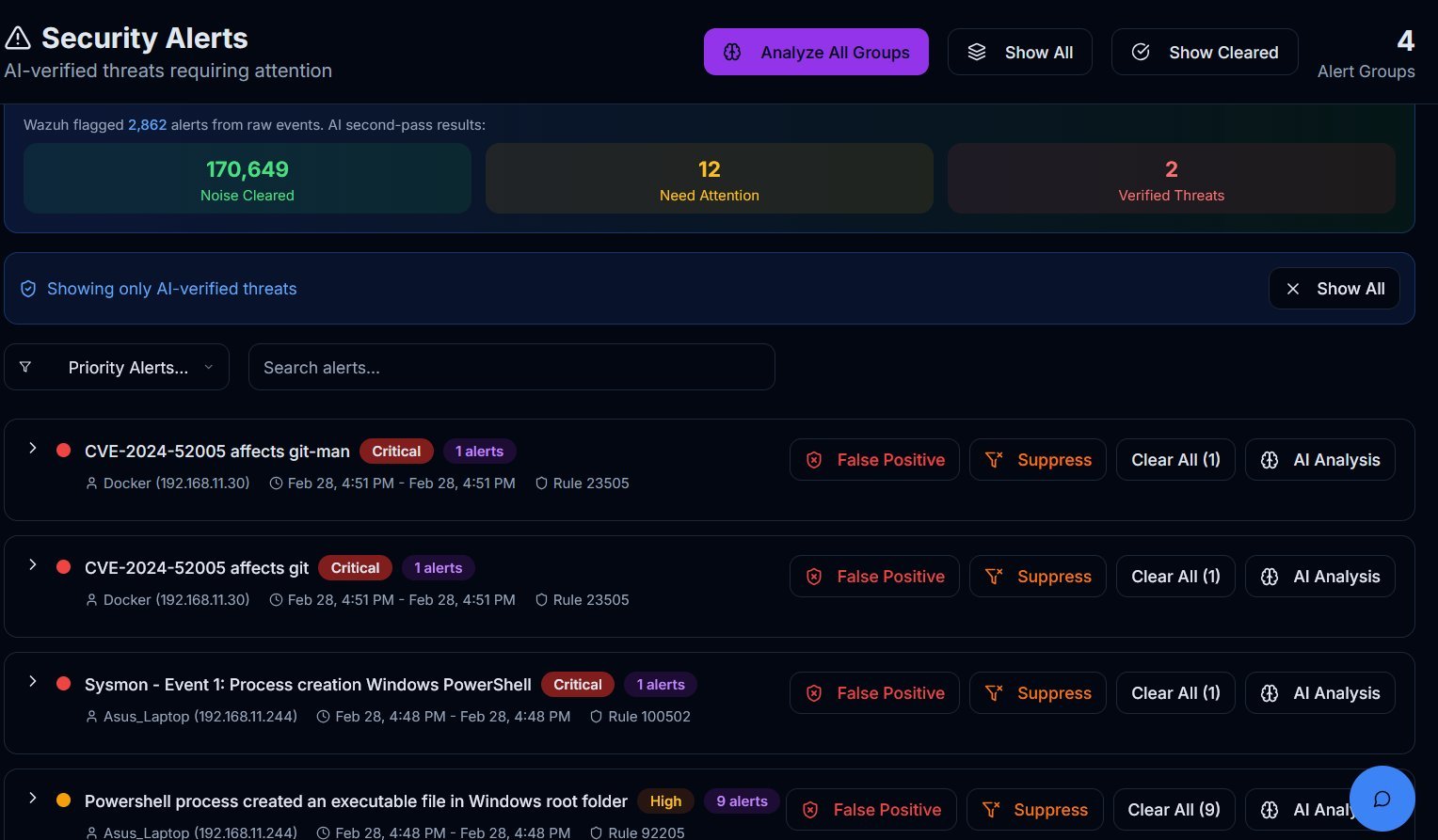
Built on Wazuh — the world's most trusted open-source SIEM — SecureSOC uses AI to automatically clear false positives, escalate real threats, and learn from your environment over time. Batch analysis processes hundreds of alert groups in minutes with full audit trails for compliance.
- Automatic false positive elimination
- Batch processing of alert groups
- Full audit trails for compliance
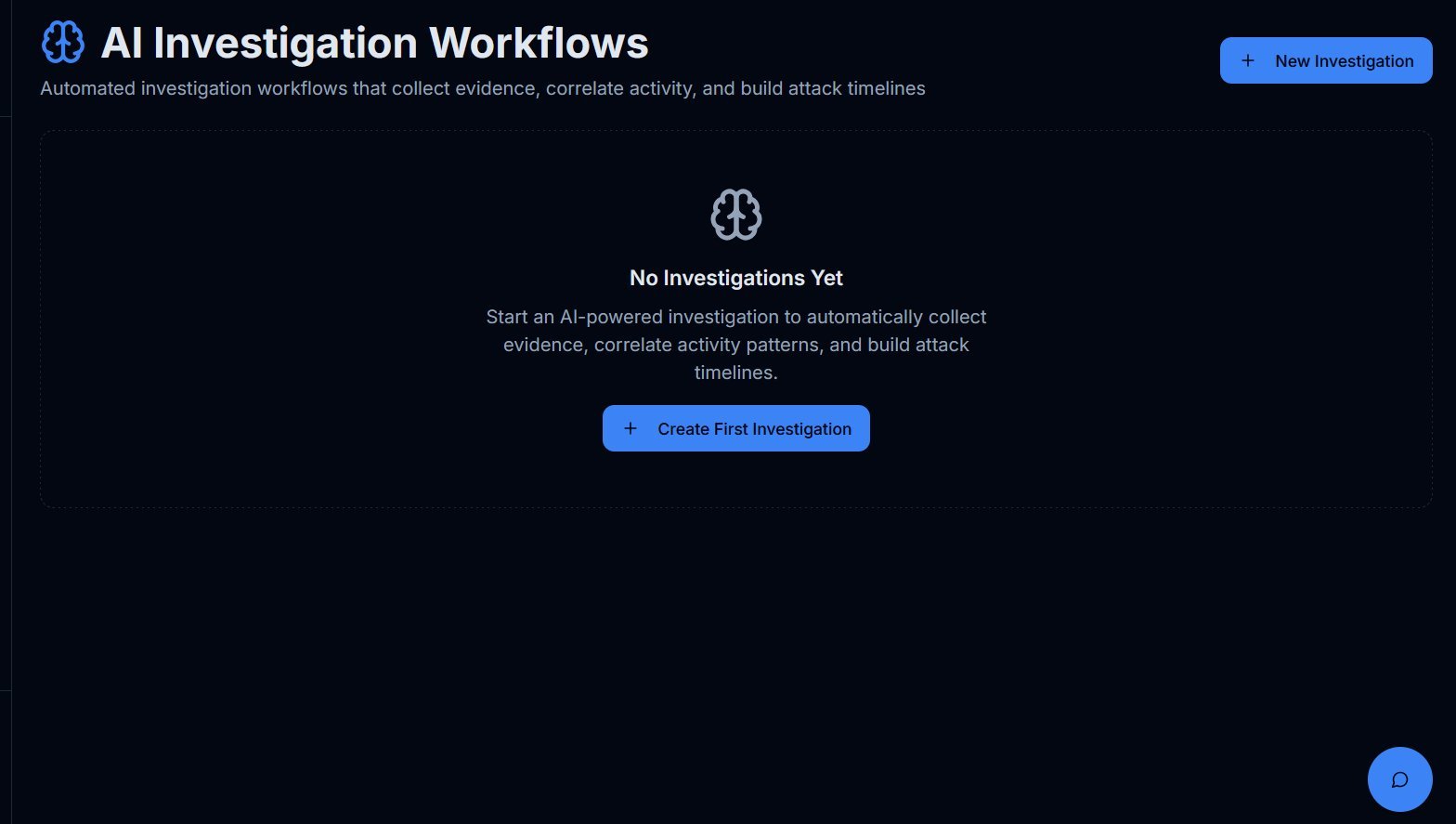
SecureSOC collects evidence, correlates activity across your environment, builds attack timelines, identifies root cause, and delivers prioritized remediation steps — with analyst oversight at every stage.
- Automated evidence collection
- Attack timeline construction
- Prioritized remediation steps
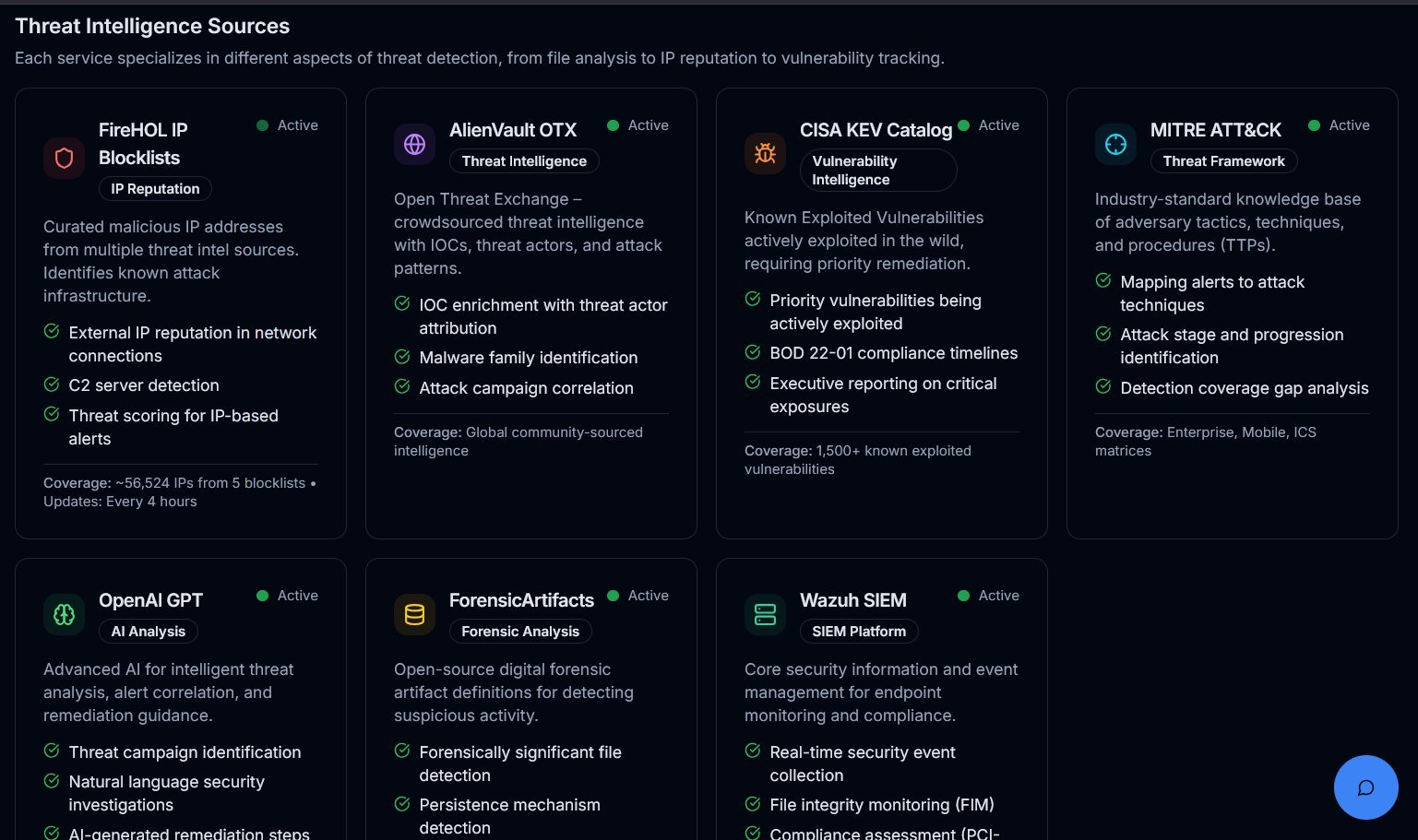
Your alerts are automatically enriched with intelligence from AlienVault OTX, CISA Known Exploited Vulnerabilities, MITRE ATT&CK, FireHOL, Spamhaus, DShield, and ForensicArtifacts. When Wazuh flags suspicious activity, SecureSOC cross-references the involved IPs against these curated databases of known bad actors — confirming indicators of compromise and helping analysts determine the severity of a threat in seconds.
- Known bad actor IP cross-referencing for threat hunting
- AlienVault OTX & CISA KEV enrichment
- MITRE ATT&CK technique mapping
- IOC confirmation accelerates investigations
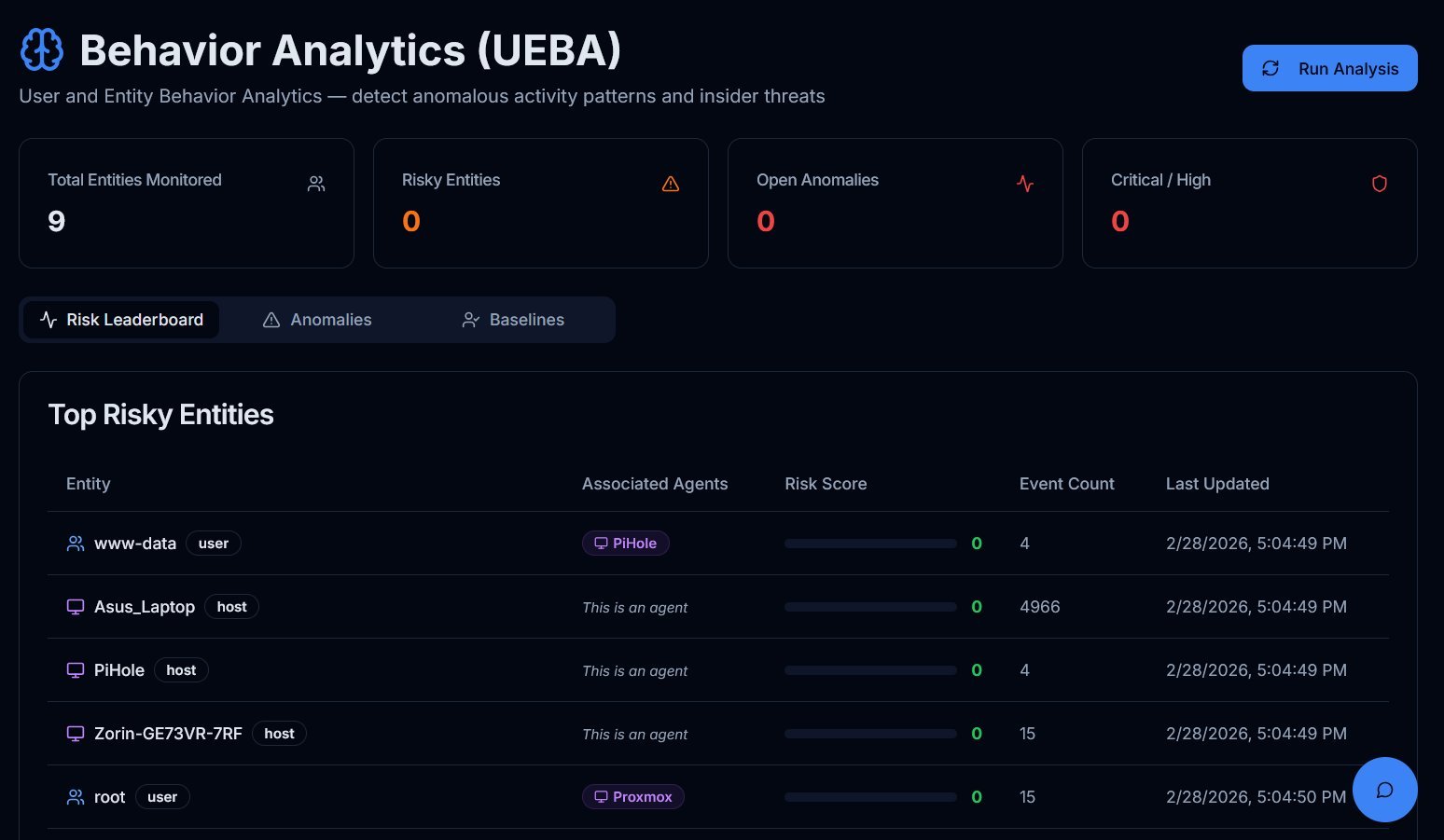
Baseline normal behavior across your network and detect anomalies like brute force attempts, off-hours access, impossible travel, and privilege escalation before they become full-blown incidents.
- Behavioral baselining
- Anomaly detection
- Insider threat identification
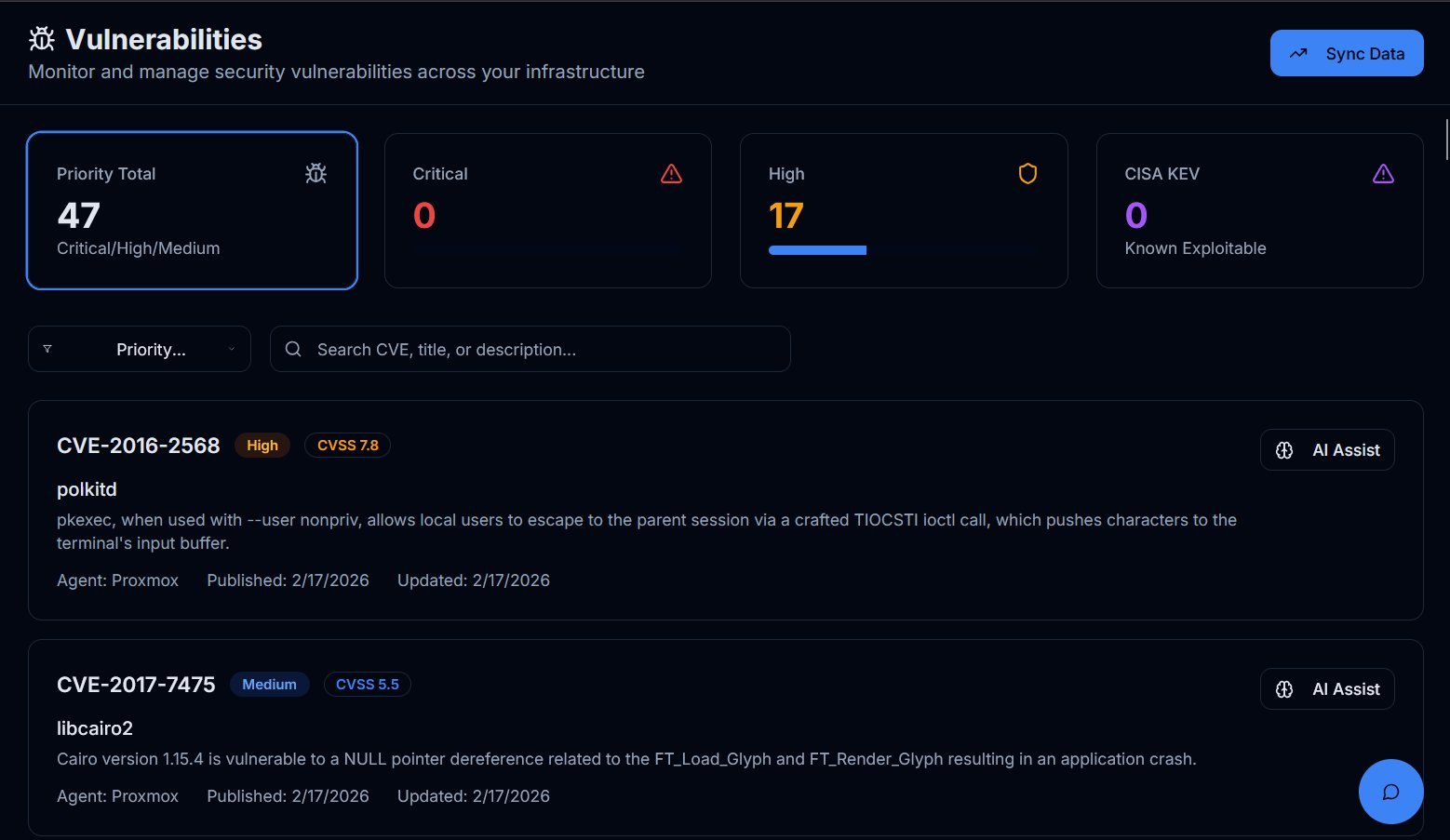
Vulnerability management is at the heart of SecureSOC. The platform continuously tracks CVEs across your environment, cross-references them against the CISA Known Exploited Vulnerabilities (KEV) catalog, and prioritizes remediation based on real-world exploitability — not just severity scores. By patching what attackers are actually targeting, you eliminate attack surface before a threat actor can take advantage of it.
- CISA KEV integration — prioritize vulnerabilities actively exploited in the wild
- Automated CVSS scoring with real-world context
- SLA-based remediation timelines with overdue tracking
- Risk acceptance workflows for vulnerabilities that can't be patched yet
- AI-generated remediation steps for every CVE
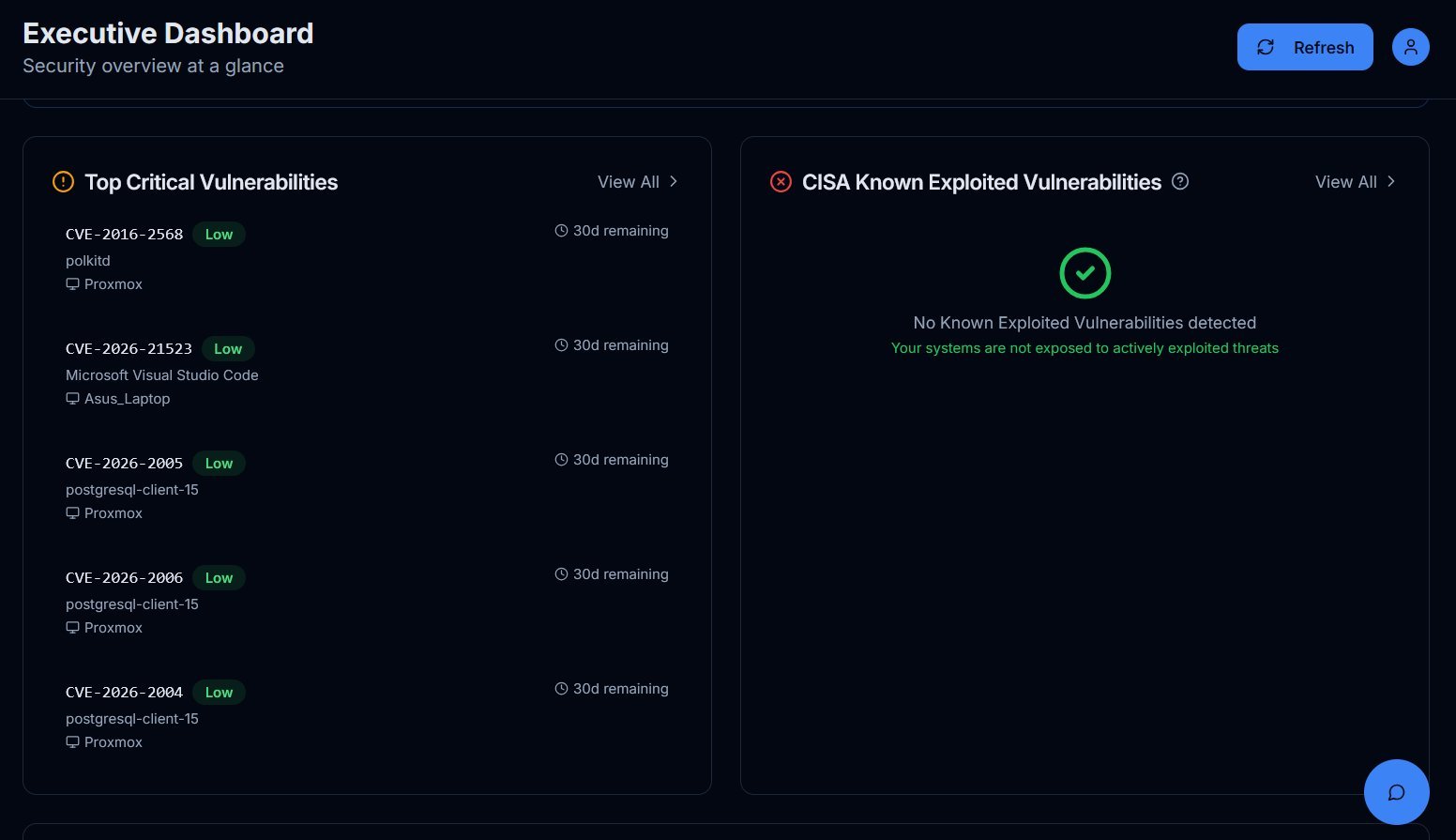
- Top critical vulnerabilities dashboard for executive visibility
SecureSOC's executive dashboard highlights your top critical vulnerabilities alongside CISA KEV status in real time. If your systems are clean of known exploited vulnerabilities, you'll see it instantly. If something needs attention, SLA timelines ensure it gets fixed before it becomes a breach. Risk acceptance workflows let you formally document and track vulnerabilities that can't be patched immediately — so nothing falls through the cracks.
- Real-time CISA KEV exposure monitoring
- Top critical vulnerabilities at a glance
- Formal risk acceptance with review timelines
- Compliance-ready documentation and audit trails
One-click PDF reports covering security posture, threat campaigns, AI efficiency metrics, vulnerability status, and compliance readiness. Built for leadership and board-level visibility.
- One-click PDF generation
- Security posture overview
- Compliance readiness metrics